This payload is most likely detected now, but it may still prove useful for research purposes.
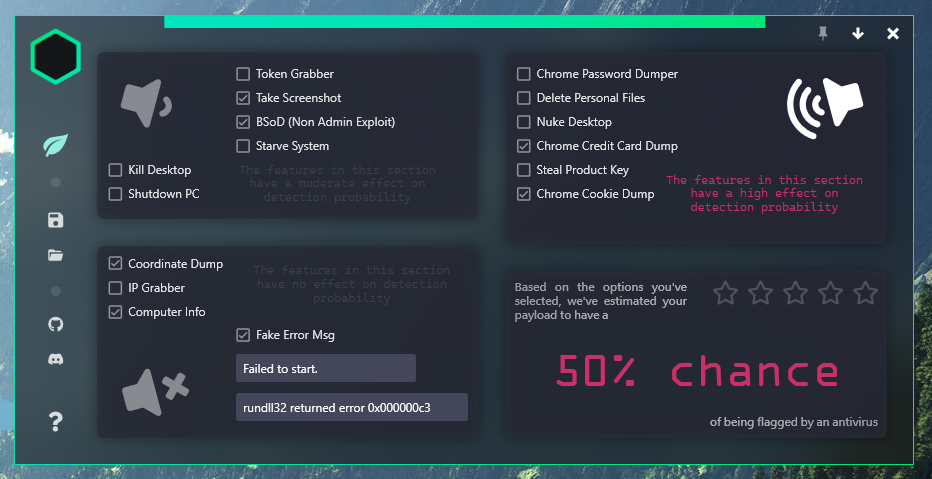
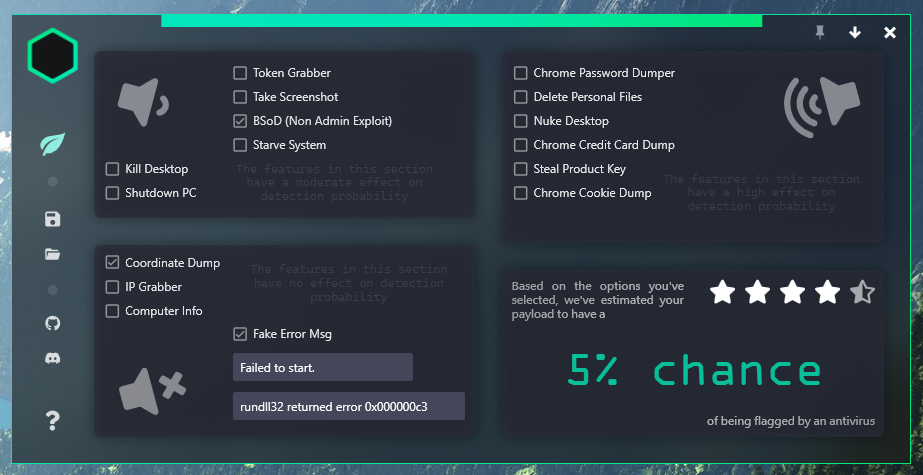
In full, Liveton is a custom payload creation tool designed for use in a penetration testing environment to obtain potentially useful information about a target, such as advanced location data, saved chromium data (passwords & cookies), Windows activation information, and a couple other useful bits of general system info. There are also a few extra bells and whistles that were meant to help potentially lower suspicion / make the payload more difficult to analyze like killing the explorer (desktop) process, displaying fake error pop-ups, triggering a Hardstop [BSoD] via NTAPI, and wiping personal file directories. This is the 3rd major evolution of this software, hence Mk3
I had plans to implement a GUI & CLI that would make generating payloads significantly easier, however this project ended up getting abandoned mid development in favor of Shield
Feel free to take a peek at the source, below are some screenshots of the non-implemented GUI, and I'll work on adding comments over the coming months.
This software was designed for usage in a secure penetration testing research environment, where all parties are fully aware of the functionality / intent of this software's user.